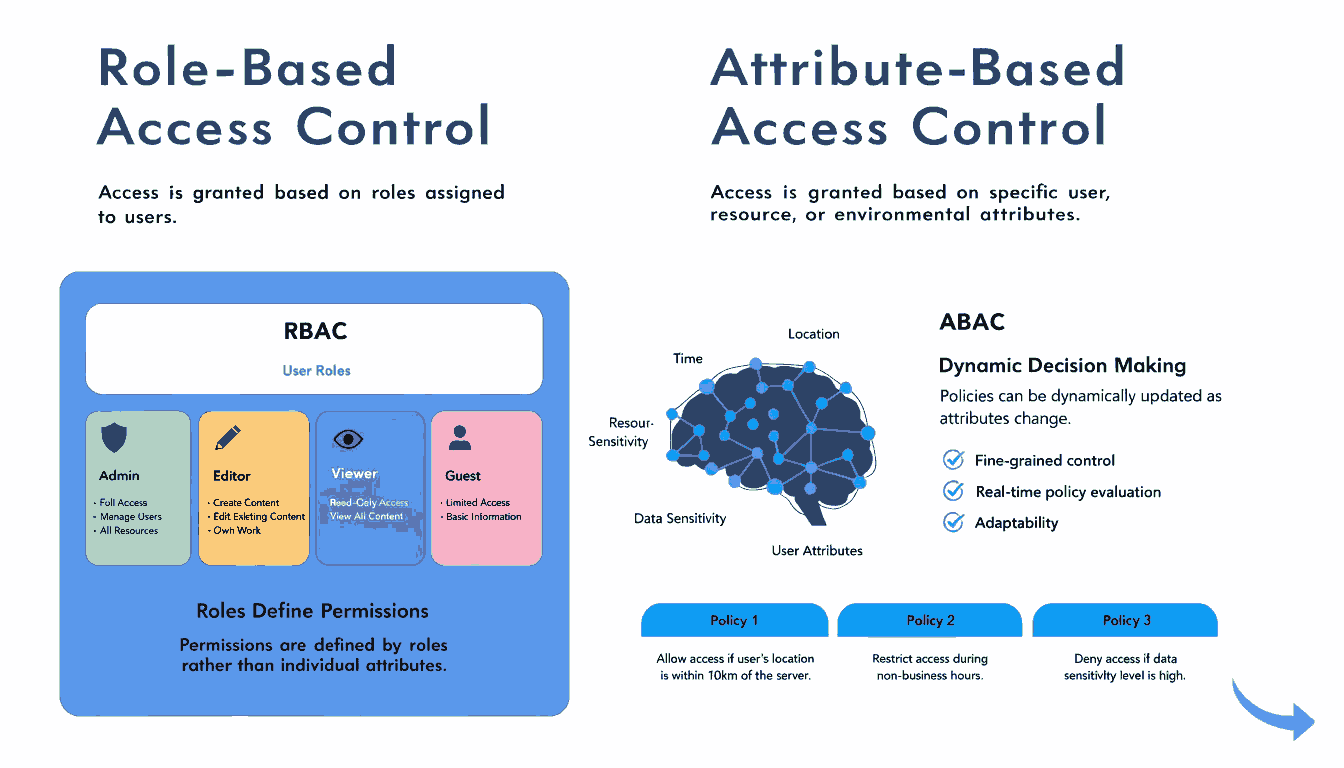
In today’s data-driven environment, managing who can access what is critical for both security and compliance. Organizations handle sensitive information across departments, systems, and geographies, making access control a foundational component of cybersecurity. Two widely used models—Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC)—offer different approaches to managing permissions.
While both models aim to restrict unauthorized access, they differ significantly in structure, flexibility, and scalability. Understanding the difference between RBAC and ABAC can help organizations choose the right framework based on their needs.
What is RBAC (Role-Based Access Control)?
Role-Based Access Control (RBAC) is a method of restricting system access based on the roles assigned to users within an organization. Instead of assigning permissions individually, users are grouped into roles, and each role is granted specific permissions.
How RBAC Works
- Users are assigned roles (e.g., Admin, Manager, Employee)
- Each role has predefined permissions
- Access decisions are based on the user’s role
Example
In a company:
- HR Manager can access employee records
- IT Admin can manage system settings
- Sales Executive can view customer data
Advantages of RBAC
- Simple to implement and manage
- Easy to audit roles and permissions
- Reduces administrative overhead
- Ideal for organizations with clearly defined roles
Limitations of RBAC
- Lacks flexibility for dynamic environments
- Role explosion (too many roles over time)
- Cannot handle context-based access (like time, location)
What Is ABAC (Attribute-Based Access Control)?
Attribute-Based Access Control (ABAC) is a more advanced access control model that grants or denies access based on attributes. These attributes can belong to users, resources, actions, or the environment.
How ABAC Works
Access decisions are made using policies that evaluate:
- User attributes (e.g., department, designation)
- Resource attributes (e.g., file type, sensitivity)
- Environmental attributes (e.g., location, time)
- Action attributes (e.g., read, write, edit)
Example
A policy might say:
Allow access to financial reports only if the user is in the Finance department AND accessing during office hours AND from a secure device.
Advantages of ABAC
- Highly flexible and dynamic
- Fine-grained access control
- Context-aware decision making
- Scales well for complex environments
Limitations of ABAC
- More complex to design and implement
- Requires strong policy management
- Can be harder to audit compared to RBAC
Where Role-Based Access Meets Purpose-Based Access
As organizations evolve, traditional access models are also adapting. A growing concept—Role-Based Access Meets Purpose-Based Access—is emerging as a bridge between RBAC and more contextual frameworks like ABAC.
This approach goes beyond simply assigning roles or evaluating attributes. It focuses on why data is being accessed. For example, even if a user has the correct role or attributes, access may only be granted if the purpose aligns with business or regulatory requirements.
Example of Purpose-Based Layer
- A marketing employee can access customer data
- But only for campaign analysis—not for exporting or sharing externally
Here, access is controlled not just by role or attributes, but by intent and purpose, adding an additional layer of governance.
This concept is particularly relevant in:
- Data privacy regulations
- Consent-driven systems
- Sensitive data environments
Key Differences Between RBAC and ABAC
RBAC vs ABAC: Which One Should You Choose?
Choosing between RBAC and ABAC depends on your organization’s structure, security requirements, and operational complexity.
When to Use RBAC
- Small to medium-sized organizations
- Clearly defined job roles
- Minimal need for dynamic access decisions
- Faster implementation required
When to Use ABAC
- Large enterprises with complex workflows
- Need for real-time, context-aware decisions
- Strict compliance requirements
- Multi-system or cloud-based environments
Can RBAC and ABAC Work Together?
Yes, many organizations adopt a hybrid approach combining both models.
For example:
- Use RBAC to assign broad permissions
- Use ABAC to refine access based on conditions
- Add a purpose-based layer to ensure compliance and intent alignment
This layered model reflects how Role-Based Access Meets Purpose-Based Access in modern systems—creating a more secure and intelligent access control framework.
Real-World Use Cases
RBAC Use Case
A hospital system assigns roles like:
- Doctor
- Nurse
- Receptionist
Each role has predefined access, ensuring quick and structured permission management.
ABAC Use Case
In a financial institution:
- Access is granted based on role + location + device security
- A manager can only approve transactions if logged in from a secure network during working hours
Hybrid + Purpose-Based Use Case
- A finance executive can access reports
- Access is limited to audit purposes only
- Data cannot be downloaded unless explicitly approved
Security and Compliance Considerations
With increasing regulations such as data protection laws, organizations must ensure:
- Least privilege access
- Auditability
- Policy enforcement
RBAC provides easier auditing, while ABAC offers stronger compliance through granular control. When combined with purpose-based access, organizations gain even better visibility into why data is being used.
Common Challenges in Implementation
RBAC Challenges
- Managing too many roles
- Lack of adaptability
- Manual updates required
ABAC Challenges
- Policy complexity
- Higher initial setup cost
- Requires skilled management
Purpose-Based Challenges
- Defining clear usage policies
- Monitoring intent in real-time
- Aligning with legal and compliance frameworks
Future of Access Control
As organizations move toward cloud computing and zero-trust security models, ABAC is gaining popularity due to its adaptability. However, RBAC remains relevant due to its simplicity and ease of use.
The future lies in convergence—where Role-Based Access Meets Purpose-Based Access, supported by dynamic attributes and policy engines. This ensures not just secure access, but responsible and compliant data usage.
Conclusion
The difference between RBAC and ABAC lies in their approach to access control. RBAC focuses on who you are (role), while ABAC focuses on what conditions apply (attributes).
However, modern systems are evolving beyond this binary choice. With the rise of privacy regulations and data governance needs, the idea of Role-Based Access Meets Purpose-Based Access is becoming essential.
If your organization values simplicity and structured access, RBAC is a strong choice. But if you need flexibility, scalability, and context-aware security, ABAC is the better option. For a future-ready approach, combining both—along with purpose-driven controls—offers the best results.
FAQs:
1. What is the main difference between RBAC and ABAC?
RBAC assigns access based on user roles, while ABAC uses multiple attributes like user, environment, and resource conditions.
2. What does “Role-Based Access Meets Purpose-Based Access” mean?
It means combining role-based permissions with purpose-driven rules to ensure data is accessed only for valid and approved use cases.
3. Is ABAC more secure than RBAC?
ABAC can provide stronger security due to its fine-grained and context-aware policies, especially when combined with purpose-based controls.
4. Why is RBAC easier to implement?
RBAC uses predefined roles, making it simpler to assign and manage permissions compared to complex policy-based systems.
5. Can small businesses use ABAC?
Yes, but it may not be necessary unless they have complex access requirements.
6. What is role explosion in RBAC?
Role explosion occurs when too many roles are created to handle different access needs, making management difficult.
7. Is ABAC suitable for cloud environments?
Yes, ABAC is ideal for cloud systems due to its scalability and dynamic access control capabilities.
8. Can RBAC, ABAC, and purpose-based access be combined?
Yes, combining all three creates a powerful, flexible, and compliance-friendly access control system.