Best of blockchain and crypto
Showing 97 - 112 of 644 Results
Best CRM Developers for Custom Business Softw...
14 May 2026
Modern businesses need smarter ways to manage customer relationships, sales operations, and internal workflows. As companies continue moving toward digital transformation, the demand for skilled crm developers is...
Building Better Search Reach With SEO for Sec...
14 May 2026
The security industry has experienced major changes as businesses and homeowners increasingly rely on online platforms to find trusted protection services. Whether customers need surveillance systems, private guards,...
AI in Automation Testing: How Intelligent Tes...
13 May 2026
The software testing industry is undergoing a major transformation. Traditional automation frameworks, while effective, often require heavy maintenance, manual scripting, and continuous updates. As applications become more complex...
Software development company
13 May 2026
A software development company plays a pivotal role in helping businesses navigate the rapidly evolving digital landscape. From startups seeking innovative mobile applications to large enterprises requiring complex enterprise...
Complete Review of Gaintools NSF to PST Conve...
13 May 2026
Running Lotus Notes database files can turn into a kind of pain when people need to read their email in Microsoft Outlook, you know. Because IBM Lotus Notes...
Advance Your Cybersecurity Career with ISO 27...
13 May 2026
Cybersecurity and information security management have become essential priorities for organizations operating in today’s digital environment. Businesses across industries are actively investing in stronger security frameworks to protect...
Services Center UAE
13 May 2026
When your home appliances stop working properly, it can interrupt your daily routine and create unnecessary stress. At Services Center UAE, we provide trusted, professional, and affordable appliance...
Are Procore Software and Tradify The Best Too...
13 May 2026
In the fast-paced world of building and infrastructure, efficiency isn’t just a luxury—it’s a requirement. At Codatis, we specialize in providing the digital tools you need to stay competitive....
How Custom Transportation Management Systems...
13 May 2026
The logistics industry is evolving rapidly, and businesses today face increasing pressure to deliver products faster while keeping transportation costs under control. Rising fuel prices, changing customer expectations,...
Top 15 Software Development Partners for Saud...
13 May 2026
Saudi Arabia is rapidly embracing digital transformation under its ambitious Vision 2030. To meet the country’s evolving tech demands, organizations are seeking top-tier partners for scalable digital solutions. Selecting...
API Design: Building Scalable and Developer-F...
13 May 2026
APIs are the backbone of modern applications. From mobile apps and SaaS platforms to AI-powered systems, every digital product relies on APIs for communication between services. A well-designed...
How 3D Product Visualization Reduces Returns...
13 May 2026
Online shopping has transformed the retail landscape but it hasn't solved one persistent, costly problem: product returns. Return rates for e-commerce hover between 20–30%, compared to just 8–10%...
How a Mobile Application Development Company...
12 May 2026
Businesses today are rapidly moving toward digital transformation to improve customer engagement, automate operations, and increase long-term growth opportunities. Mobile applications have become one of the most important...
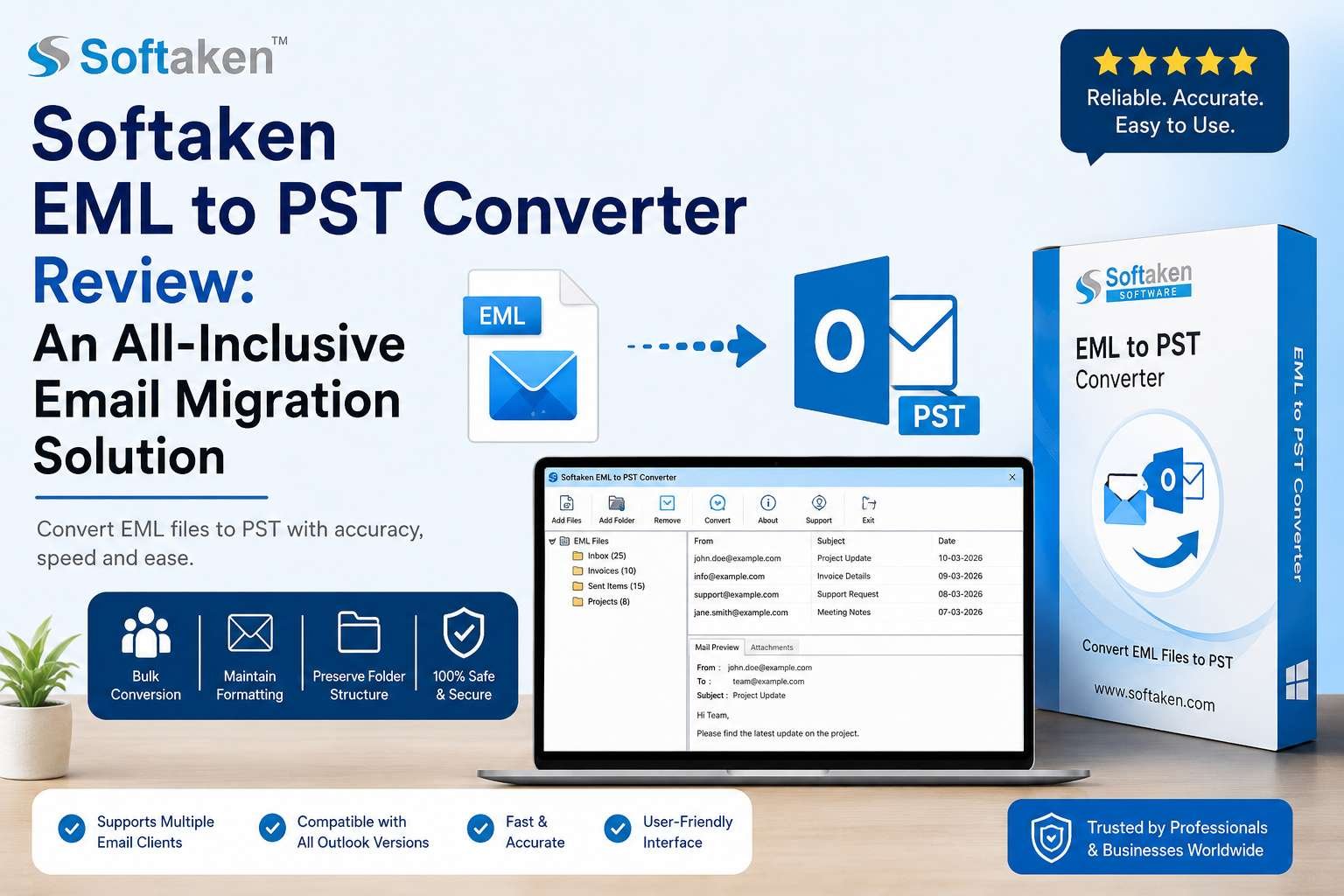
Softaken EML to PST Converter Review: An All-...
12 May 2026
IntroductionWhen moving from email programs like Outlook Express, Windows Live Mail or Mozilla Thunderbird to Microsoft Outlook, many users eventually faces the issue of email transfer. Transferring hundreds...
Strategic SEO for Counselors by Digital Trium...
11 May 2026
In today’s digital-first world, counselors need more than professional expertise to grow their practice—they need visibility where potential clients are actively searching for help. This is where a...
Hotel POS Software Development: A Complete Be...
11 May 2026
In today’s fast-evolving hospitality industry, technology plays a major role in improving customer experience, streamlining operations, and increasing revenue. One of the most essential tools for hotels is...